Uncategorized
Severe vulnerability exposes WordPress websites to attack
A severe WordPress vulnerability which has been left a year without being patched has the potential to disrupt countless websites running…
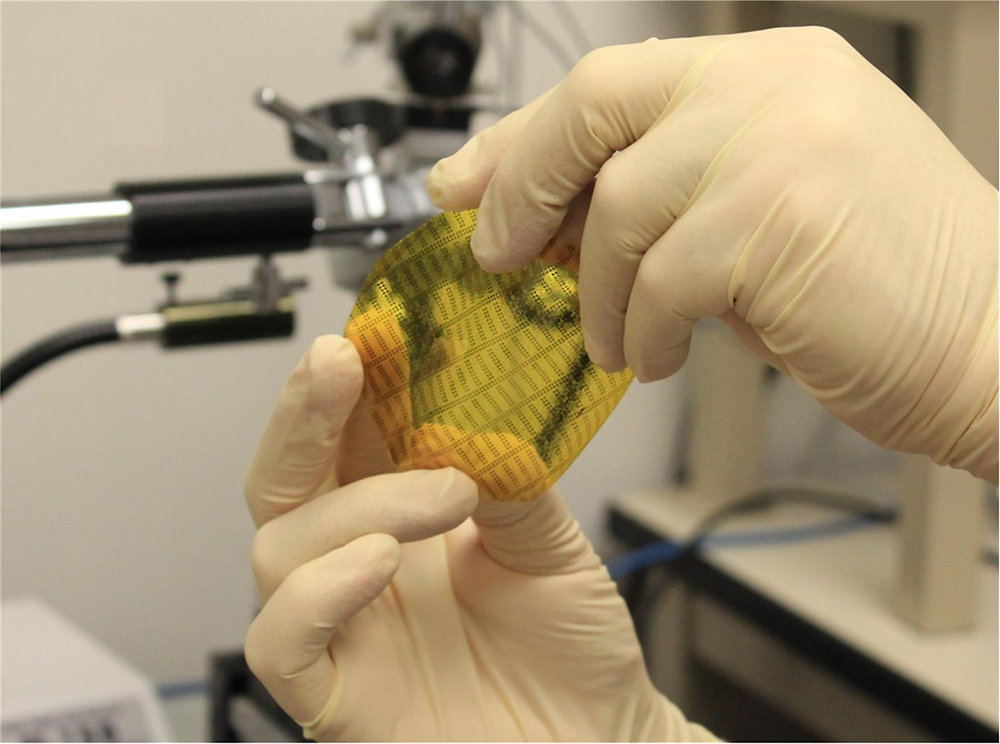
Read MoreHairy artificial skin gives robots a sense of touch
Hairy robots could be more sensitive to touch than humans. Researchers at the University of Texas at Arlington have patented a new…
Read MoreNew ransomware arrives with a hidden feature that hints at more sophisticated attacks to come
A new form of ransomware is spreading to victims around the world and the way it’s built suggests those behind it could use it to launch…
Read MoreDigital transformation lives or dies in the data centre
Last time, we looked at the role of the network in campus management, and how Fabric Networking powers digital transformation by enabling…
Read MoreFabric networking: Be more responsive to your business
In blog 1 of this five-part series, we saw that digital transformation requires faster, more flexible, and secure networks. In this post,…
Read MoreHow to protect your privacy in Windows 10
There has been some concern that Windows 10 gathers too much private information from users. Whether you think Microsoft’s operating…
Read MoreNotPetya malware attack: Chaos but not cyber warfare
The impact of last year’s NotPetya cyber attack was felt around the world, bringing several large organisations grinding to a halt…
Read More5 things we love about Extreme’s network fabrics
Last time, we explored the evolution of networking. And back in the second post in this blog series on fabric networking, we saw how…
Read MorePhishing scam claims recall on exploding Barclays credit cards
Scammers are taking phishing attack low tech in a scheme targeting Barclays customers, claiming that a recall has been issued for…
Read MoreGhostscript flaw could allow attackers to take remote control of systems – and there’s n
A vulnerability in Ghostscript, a widely used interpreter for Adobe PostScript and PDF page description languages, could allow attackers…
Read More