Uncategorized
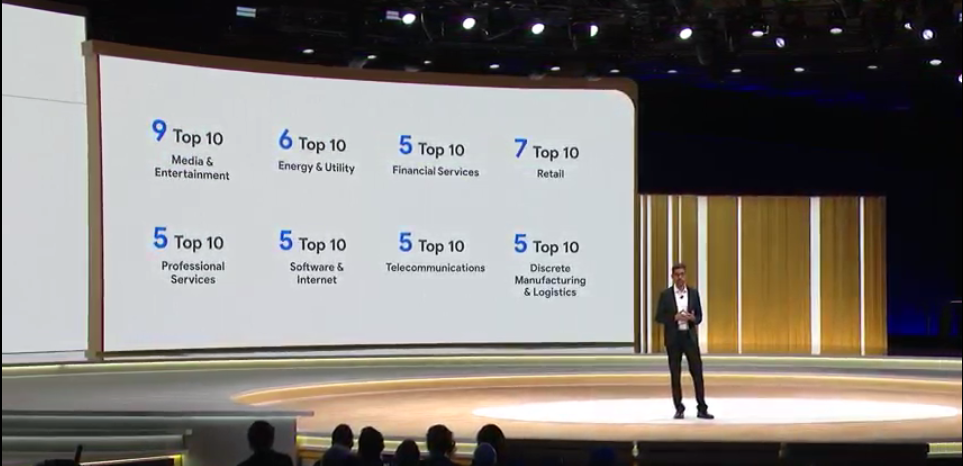
Google Cloud Next: Everything you need to know about the new strategy
Google Cloud Platform CEO Thomas Kurian made his debut as leader of the company and outlined a strategy that will look familiar to…
Read MoreA PEEK INTO THE TOOLKIT OF THE DANGEROUS TRITON HACKERS
When the malware known both as Triton and Trisis came to light in late 2017, it quickly gained a reputation as perhaps the world’s most…
Read MoreWhat’s next for data centers? Think micro data centers
The death of the corporate data center may be a bit premature. Yes, enterprises are going cloud, but the data center could become…
Read MoreTajMahal cyber-espionage campaign uses previously unseen malicious tools
A newly discovered form of malware deployed as part of a highly stealthy cyber-espionage campaign comes with several new malicious…
Read MoreThe role of IT in the cloud era
New innovations such as the cloud and increased security risks have changed the role of the IT department drastically over the last few…
Read MoreDell Technologies extends systems integrator agreement with Cisco
Dell Technologies on Monday announced a multi-year extension of its systems integrator agreement with Cisco, demonstrating Dell’s…
Read MoreOracle security warning: Customers told to patch ASAP to swat 297 bugs
Oracle is urging customers to install its April critical patch update to protect themselves against attackers who are targeting firms…
Read MoreFCC eyes blockchain to track, monitor growing wireless spectrums
CAMBRIDGE, Mass. – The need for new Wi-Fi spectrums is expected to grow as infrastructure becomes increasingly more connected through IoT…
Read MoreServerless computing growth softens, at least for now
After much excitement about serverless computing — seen as the next evolution of cloud — IT professionals have lately taken a more…
Read MoreThe future of cybersecurity: Your body as a hacker-proof network
What do insulin pumps, pacemakers, and MRI scanners have in common? If you said they’re all medical devices that can help to save your…
Read More