Uncategorized
SMB security pack: Policies to protect your business
Small and midsize businesses are increasingly being targeted by cybercriminals—but they often lack the resources and expertise to develop…
Read MoreGreyEnergy: New malware campaign targets critical infrastructure companies
The hacking group which took down Ukrainian power grids is systematically targeting critical infrastructure in Ukraine and beyond in what…
Read MoreSecurities market participants face greatest financial cyber threat: BAE Systems
The securities markets — trading in stocks, bonds, equities, debt, derivatives, and the like — face the highest level of cyber threat of…
Read MoreIs your cloud provider lying to you? A guide for SMB’s.
Whatever industry you’re in, you tend to forget that what seems obvious to you is Greek to someone who isn’t in the same game. In IT…
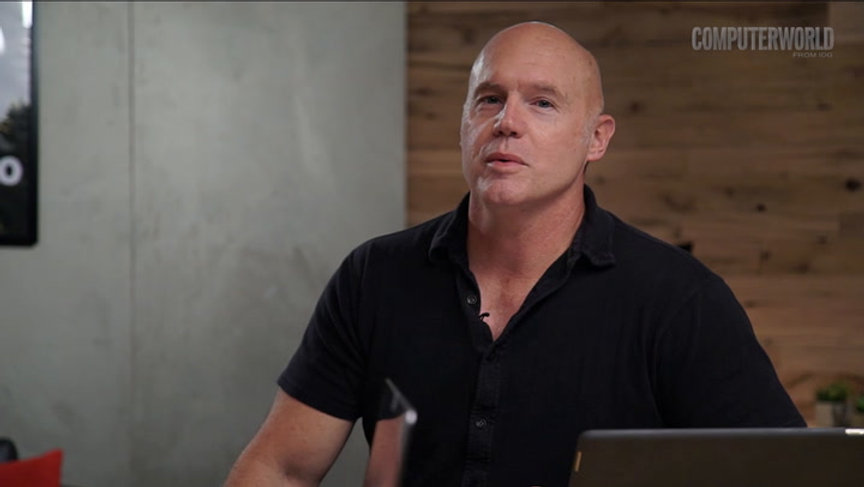
Read MoreMingis on Tech: Data breaches and the rise of ‘surveillance capitalism’
Data breaches have become so common, and so frequent, that when companies like Facebook or Google admit to data leaks or outright hacks,…
Read MoreThe dynamic nature of trust in the digital age
Business thinker and author Rachel Botsman reveals how technology is impacting the way we trust, and the opportunities and consequences…
Read MoreTwo New Bluetooth Chip Flaws Expose Millions of Devices to Remote Attacks
Security researchers have unveiled details of two critical vulnerabilities in Bluetooth Low Energy (BLE) chips embedded in millions of…
Read More‘A cyber-attack could stop the country’
Superfast 5G mobile broadband could power smart cities and the internet of things, (IoT) but as more devices get connected, telecoms and…
Read MoreNew Intel CPU Flaw Exploits Hyper-Threading to Steal Encrypted Data
A team of security researchers has discovered another serious side-channel vulnerability in Intel CPUs that could allow an attacker to…
Read MoreSecurity guarantees will be meaningless under encryption-busting laws: Senetas
Australian security vendor Senetas has called for the proposed Assistance and Access Bill to be withdrawn, saying it will damage…
Read More